Recently I introduced Threat Intel Query (tiquery), a multi-source threat intelligence lookup tool. The first iteration expanded on the capability of malhash and enabled for the submission of malware hashes against multiple threat intel sites.
Then yesterday I was targeted with an SMS phishing message. (Note: I don’t know why but I detest the term ‘smishing‘, or any of the other ‘ishings that have been used to describe these tactics.) The message was one of those outstanding traffic violations ‘Final Court Notice’ type scare tactics. Instead of a URL it had a QR code.
This inspired me to add some additional capability to tiquery. I’ve added URL support, that will query against VirusTotal, urlscan.io and Google Safe Browsing. As with all the other sources, API keys are required.
I also added a QR decoding capability, so you can browse to a screenshot of a QR code and tiquery will decode it, and then submit the URL to the Threat Intel lookups.
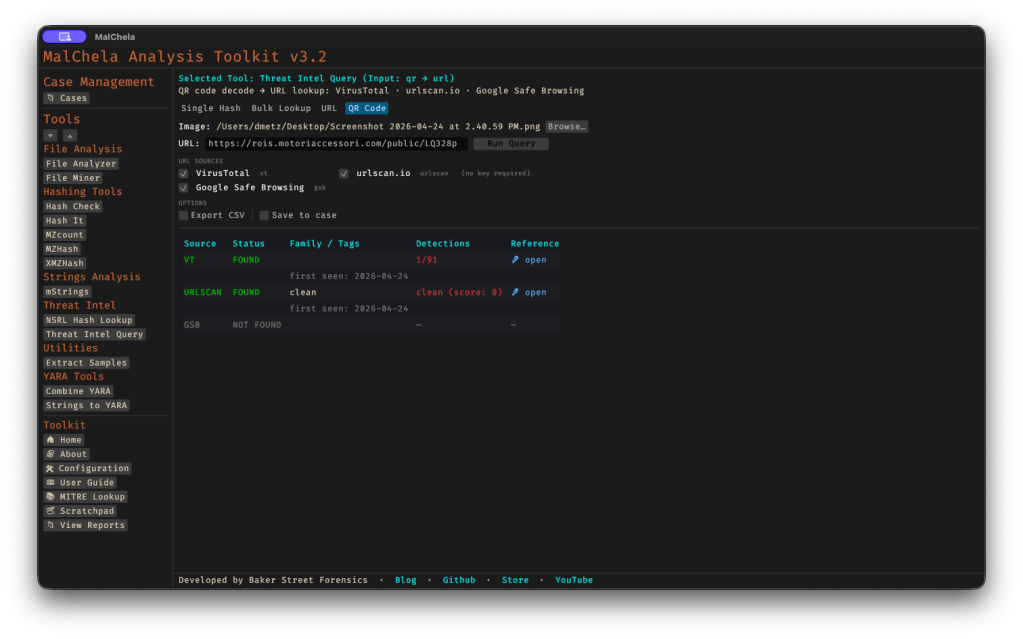
This was a fairly new sample and the url had been created just hours before.
Version 3.2.1 also adds the ability, when you’re in hash submission, to browse to a file. Only the hash, not the file, gets submitted – it just combines two steps into one.
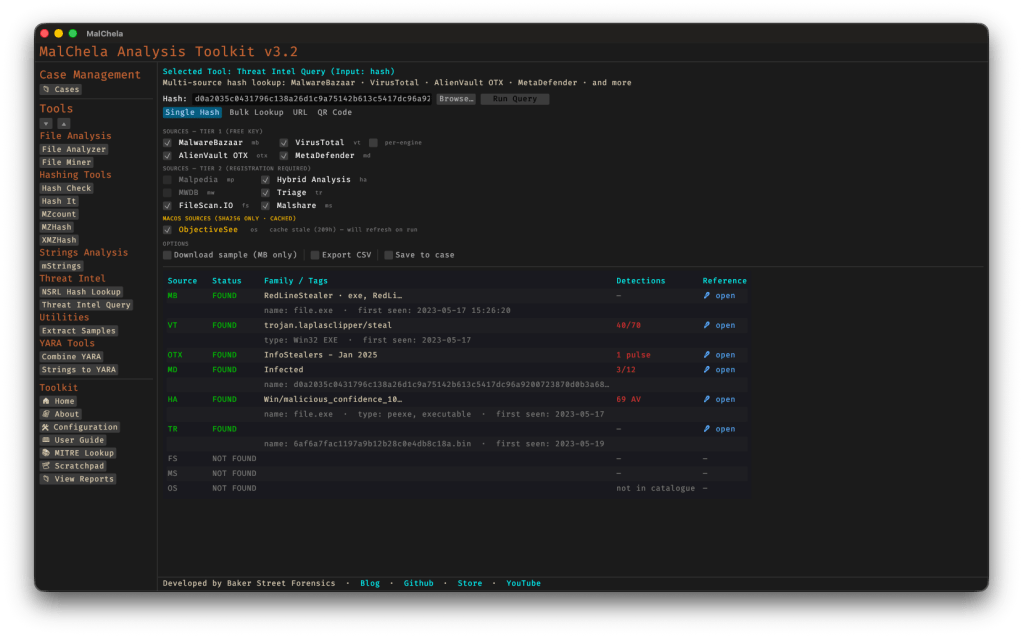
Support for Recorded Future Tri.ge (researcher account) has also been validated. On that note, if you’re a member at Malpedia and would like to send me an invite, it would be much appreciated.
You can find the full documentation for tiquery including command line syntax in the User Guide within MalChela, or via the online docs here.

One thought on “From QR to Threat Identification in one Click”